|
Other than remote login, there's various useful things you can do with ssh, like running a remote command, multiplexing connections to save on server resource, setting up ssh aliases to save you some keystrokes, and so forth. Recently, when my partner logged on a recently created CentOS server hosted at Digital Ocean, he saw the following messages: Last failed login: Tue Jul 29 16:27:31 EDT 2014 from stuff2share.net on ssh:notty Clearly that wasn't us trying to log in. Obviously, there was some malicious user(s) likely trying to enter our server with brute-force attacks. We were under a ssh brute force attack. Such malicious scan is not uncommon these days. It came just a couple days after our new server was up.
I learned a few good ways to prevent this:
0 Comments
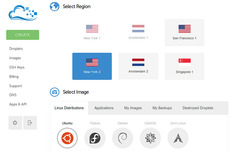 Looking for a hosting service? For about 55 seconds, Digital Ocean said that's how long it'll take them to provision a server. That sounds effective, and the cost is relatively low compared to others, making it a cost-effective option. Create A Virtual Server I signed up at Digital Ocean, requested a server with CentOS, and chose Singapore region for hosting the image since that location in Asia is closer to one of my projects' target audience. It took 58 seconds wait time for creating the image. It lives up to the promise. Immediately, in my email box I received the IP and the root password so I can access the virtual host remotely via SSH. |
Categories
All
Archives
May 2020
|
 RSS Feed
RSS Feed