|
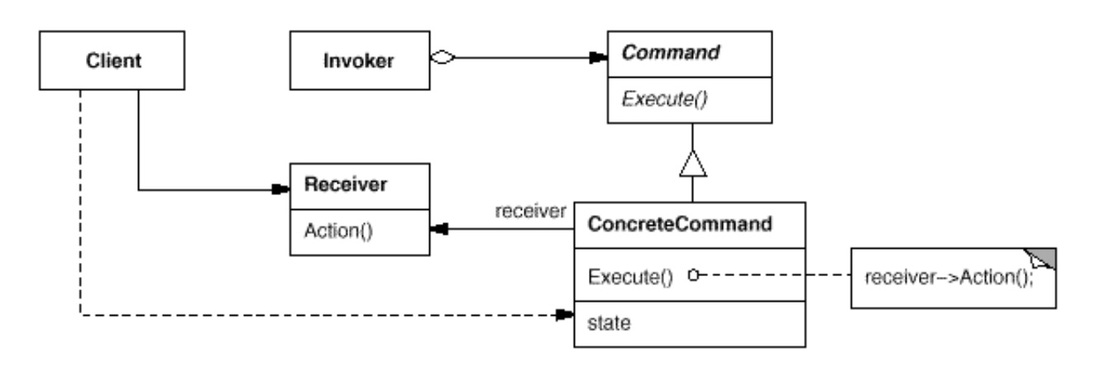
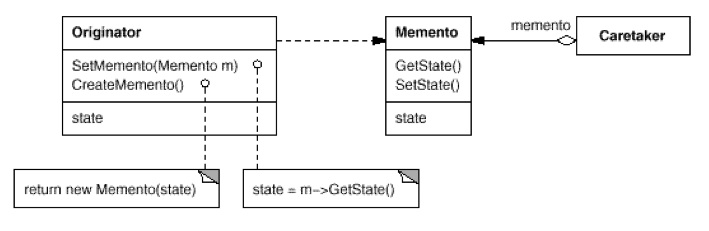
In a Composite (or Decorator) structure, Prototype uses a prototypical instance to create new Composite Component. Composite is a structural pattern where as Prototype is creational pattern. They are related to each other in a sense that Prototype only make sense in the context of a structural pattern like Composite or Decorator. 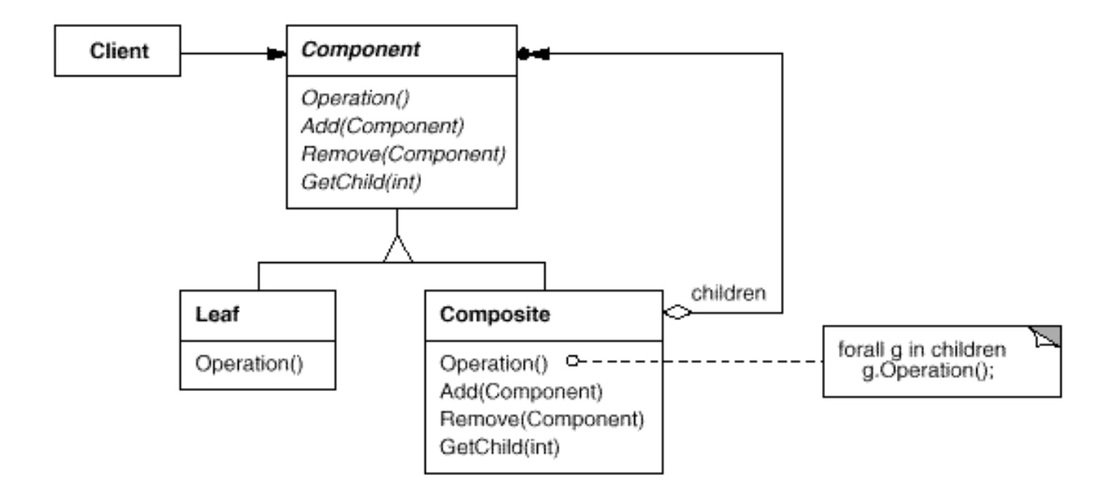 Composite (source: GoF) 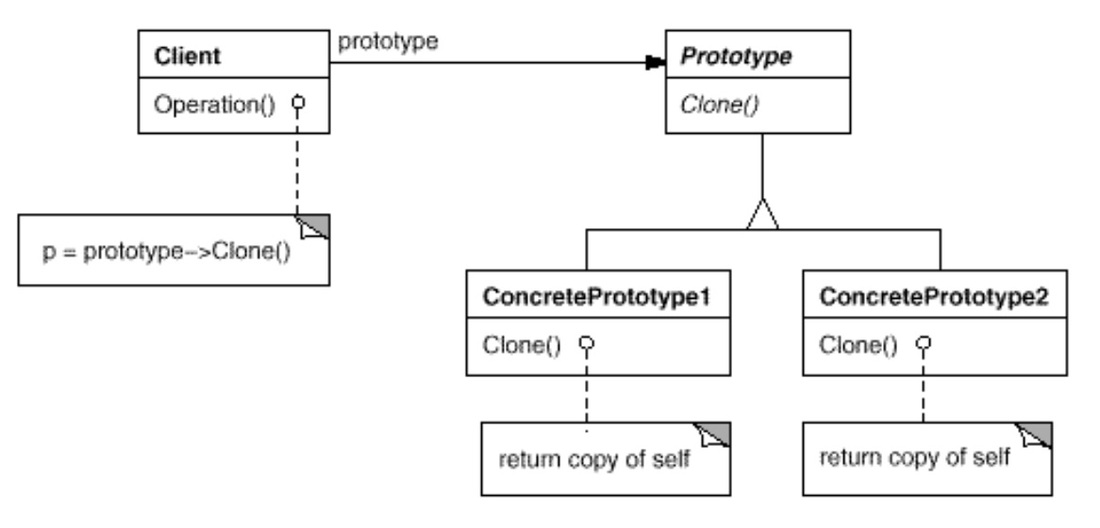 Prototype source: GoF Command pattern is a behavioral pattern in GoF as it allows us to decouple between the Invoker (a.k.a. sender, an object that invokes an operation) and the Receiver (an object that receives the request to execute a certain operation).
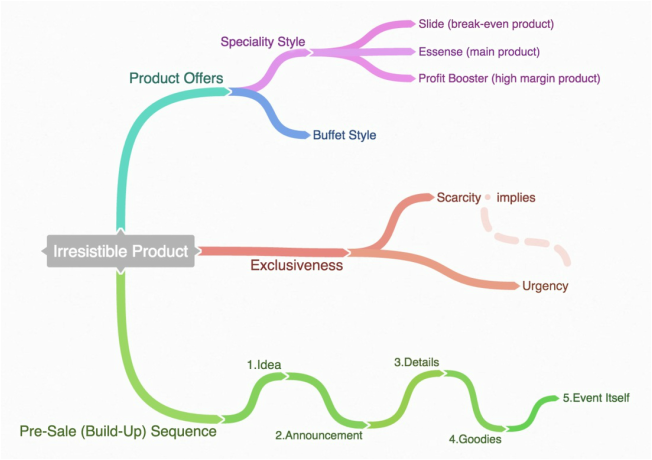
Also known as an action or transaction pattern. Getting traction is hard. In the Bullseye Framework, the outer ring is what's possible, the middle ring is what's probably, the inner ring is what's working. Getting traction is finding the inner ring.
There are 19 channels you can use to gain traction. According to Law of Shitty Clickthrough, all marketing strategies eventually result in shitty clickthrough rates. However, some may works well, others not so well. It's hard to predict which channel will work the best. Therefore, do not only consider those channels you're comfortable with. Asking your potential customers to email someone they know with your product information is difficult. In order to provide an incentive for them to do so, you can promise a free gift to the one sending out the email to one of his/her friend. The friend who gets to know your product that his/her friend suggests, and the products mentioned in the email get promoted.
The all-win situation is a great way of marketing your product. Make sure your product is good enough so you won't let the sender down. Also, make sure the gift is worth the sender's effort while you minimize the work of composing the email for the sender to send out. How? Use "mailto:" HTML tag to pre-compose the email, set the b.c.c. to yourself so you also get a copy every time the email gets sent out. Then, you process one email a time to deliver the gift to the sender. Here's an real case example I just received using this approach: the challenge
Earlier last week, I was asked to implement an in-memory database similar to Redis (name-value pairs). This post is about code style, algorithmic performance, and thought process. For simplicity's sake, my program to the challenge will receive commands via stdin, and should write appropriate responses to stdout.
I come across a list of interview questions on the web for interviewing software engineers, or specifically, for coders.
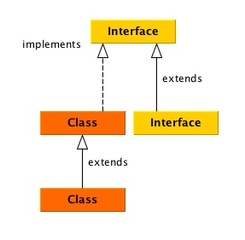
What's the differences among a software engineer, a software developer, a programmer, and a coder? It's arguable what constitutes a good developer. To me, it's the curiosity and the ability inside a developer to find and implement cost-effective software solutions that are easy to be extended by others. Knowing answers to the list below does not demonstrate the core ability of what I believe a good developer should have. Coding ability is only partially relevant to become a good software developer. There are other factors like the ability to identify the problem, the ability to provide solution, and the ability to allow others to understand your thought process so that they can extend/maintain your code easiily. Java Collection Framework (java.util.* package) is a unified architecture for representing and manipulating collections. This post is a quick note of my knowledge about Java Collection Framework that covers frequently used java data structure to store a group of elements and/or key-value pairs. In the java.util framework, there are two major camps - Collections & Map.
To illustrate, I use solid lines to denote 'extends', and dash lines to denote 'implements'. The way to use my note is to first go to the diagram looking for the specific class or interface, then read the brief blurb that'll remind you what the class or interface is about for the right data structure. |
Categories
All
Archives
May 2020
|

 RSS Feed
RSS Feed